Developed by veterans with decades of service, Sandboxx provides service members and their families the tools and support needed to confidently navigate the transitions that will be made throughout their entire military journey. Success at Sandboxx begins with our top priority, security. As soon as a user signs up and creates an account with Sandboxx we actively monitor and ensure that your information is secure and remains secure. Below is an explanation of how we protect your information so that you can feel confident that your personal details, and more importantly your service member’s details are protected.
To begin let’s first talk about Operational Security (OPSEC) and Personal Security (PERSEC).
OPSEC
The protection of critical information deemed mission essential from military commanders, senior leaders, management or other decision-making bodies.
You should never send OPSEC or critical information through the mail, Sandboxx or other non-secure electronic communications.
Examples of critical information are:
- Details on a specific mission.
Example: Information on a troop’s movement during deployment. - Details containing a location and/or time of a deployment.
Example: Using a deployment countdown app or discussing the length of a deployment on social media or around others. - Details revealing personnel information
Example: Revealing to others about a service member’s security clearance that they may have. - Details about a specific unit.
Example: Posting any information in regards to a specific military unit.
*Recruit names and basic training mailing addresses are not deemed critical information by the command. Thus using Sandboxx is not a violation of OPSEC.
PERSEC
Protecting any personal information in regards to your service member as well as yourself and family.
Examples of PERSEC are:
- Rank
- Addresses
- Family Information

So how does Sandboxx ensure that your PERSEC is secure?
We are vigilant in hardening all software components to protect our users from attacks and threats. Sandboxx’s security infrastructure is built with many risks in mind and every feature in the app is built with security and privacy at the front and center.
1. Sandboxx Data at Rest is encrypted & obfuscated
The three states of data are:
- Data in use. Active data under constant change
- Data in motion. Data that is traversing a network or residing on a mobile device to be read or updated
- Data at rest. Inactive data
What does this mean? User data regardless of what state it is in is protected even if the phone is lost or stolen.
2. Sandboxx connect to the cloud using Transport Layer Security (TLS)
Transport Layer Security (TLS) is a cryptographic protocol that provides communications security over a network. We use TLS to secure all communications between the app and our servers.
What does this mean? Network transactions are protected from packet sniffing algorithms.
3. Sandboxx packets are not attributable
What does this mean? Users are protected from man in the middle attacks.
Man-in-the-middle attack:
An attack where the attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other.
4. All data integration with other services happens on the backend
What does this mean? Users’ PII/PCI is protected and all payment information is securely handled.
PII – Personally identifiable information is information that can be used on its own or with other information to identify, contact, or locate a single person, or to identify an individual in context.
- User accounts are private by default. Only people approved by the user can see their posts, likes and comments.
- Parts of the address are intentionally masked to protect the user’s personally PII/PCI identifiable information.
- We use Stripe/PayPal to process payment information for checkout.
Stripe/PayPal/Apple Pay/Android Pay have been audited by a PCI-certified auditor, and is certified to PCI Service Provider Level 1. This is the most stringent level of certification available.
5. API & DATABASE SECURITY
Data is securely uploaded/downloaded to our servers via SSL endpoints using the HTTPS protocol. Only object owners have access to data resources. We use Server Side Encryption (SSE) to encrypt data stored-at-rest. Our server provides the encryption technology for both SSE and SSE-C. Our servers are SSAE-16 cloud security certified. Our servers have built in protection against Query Injection, Cross Site Scripting and Cross Site Request Forgery
Security is Sandboxx’s number one priority. We are vigilant in hardening all software components to protect our users from attacks and threats. To ensure your information as well as your service member’s information is secure Sandboxx’s security infrastructure is built with many risks in mind.
PERSEC Guidelines to follow
Your personal information as well as your service member’s personal information is guarded and protected with Sandboxx, but to help you stay PERSEC compliant we’ve put together a list of events that can break PERSEC and should be avoided while in the military.
Geotagging on social media.
“Checking-in” or marking your location on a picture or post that is published on social media shares your exact location with all of your 500+ “friends” on social media. Most likely 95% of those “friends” do not need to know you or your service member’s location whether it be your house, base, training location, etc.
Sharing that your service member is deployed or in the field.
Although it is hard to resist at times, refrain from publicly sharing that your service member is going to be or is currently deployed/is in the field for training. Whether posting within Sandboxx or on other social platforms, this information is is unnecessary for people to know about and does not need to be made public, including sharing the number of days until their deployment or training is over.
Pictures of your service member in uniform.
If you are going to share pictures of your service member in uniform online or within the Sandboxx app it is highly encouraged to blur/cross out/remove your service member’s name and rank from their uniform. Name and rank are considered PII and you should do your best to keep that information from becoming public knowledge to those that do not need to know.
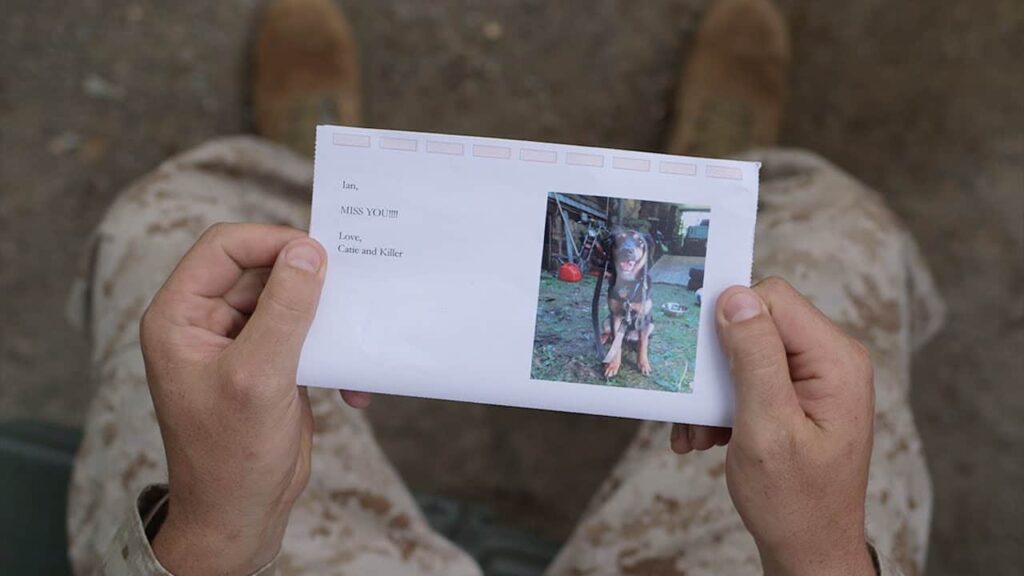
Photos of Letters with names and or addresses on them.
Here at Sandboxx we know that getting Letters from your service member is one of the greatest things to come home to, but we highly discourage you taking pictures of your envelopes (that reveal your service member’s name, rank, and address) and posting them onto social media. If you do want to share and express your happiness of receiving mail just make sure you blur/cross out/remove that detailed information
Using descriptive hashtags in your social posts.
Instagram, Twitter, Facebook, and even Sandboxx are all great social platforms to connect with friends, family members, and people from around the world, but if you are not careful are also a great way to share a lot of personal information with people you don’t know. Whether your service member is deployed, in training, or even home with you, posting pictures/tweets/statuses with descriptive hashtags can reveal whether your service member is deployed, where you are located, if you are a spouse/significant other, and what unit your service member is in. All of that information can be used by strangers and put you or your service member in danger. Examples of hashtags to avoid using are:
#DeploymentDate
#CampPendleton
#FortBenning
#NavyWife
#AirForceGirlfriend
#DeploymentSucks
#USSRushmore
#934AirliftWing
It might seem crazy or unrealistic to follow these guidelines but at the end of the day remember that your service member’s safety and your safety is most important. Publicly sharing personal information is for no one’s benefit and could potentially put you in harms way, and just because others are doing it does not always mean it’s ok.
Learn more about how Sandboxx ensures your privacy when sending Letters by reading about our Letters process.