US Special Operations Command launches investigation to discover how sensitive info was leaked online
- By Steve Balestrieri
Share This Article

The U.S. Special Operations Command (SOCOM) has launched an investigation this week to find out how it left an exposed email server that was leaking sensitive but unclassified emails online. The leak was discovered in early February after a cybersecurity researcher alerted the command.
Special Operations Command spokesperson Ken McGraw told CNN in an email that SOCOM had “initiated an investigation into information we were provided about a potential issue with the command’s Cloud service.”
“The only other information we can confirm at this point is no one has hacked US Special Operations Command’s information systems,” McGraw added.
SOCOM has troops forward deployed in dozens of countries worldwide on any given day.
The leak was discovered by Anurag Sen, a good-faith security researcher whose specialty is discovering sensitive data that is left unprotected online. He alerted TechCrunch about it so that they could alert the military and SOCOM.
Sen discovered that the SOCOM server was packed with military emails, some of which were several years old and contained sensitive personnel information. One of the most potentially damaging files included a completed SF-86 questionnaire.
Related: A deep look at the SIG Rattler, SOCOM’s new personal defense weapon
The SF-86 questionnaires are 136 pages long and can be used to conduct security clearance investigations for individuals (government employees, contractors, and military) who require access to classified information. The form also determines an individual’s eligibility for access to other sensitive information or programs. SF-86 questionnaires contain significant background information on security clearance holders that would be valuable to foreign adversaries.
It appears the leak was caused by a misconfiguration attributed to human error.
The misconfiguration with a Department of Defense (DOD) server hosted on Microsoft Azure’s government cloud allowed the email server to be accessed without a password. Yet, the server did not contain any classified material, as SOCOM classified networks are not accessible from the internet.
A spokesman for the U.S. Cyber Command (CYBERCOM) answered a query from The Hill stating that “As a matter of practice and operational security, we do not comment on the status of our networks and systems. Our defensive cyber operators proactively scan and mitigate the networks they manage.”
“Should any incidents be discovered during these regular operations, we fully mitigate, protect, and defend our networks and systems. Any information or insight is shared with relevant agencies and partners if appropriate,” the spokesman added.
Feature Image U.S. Air Force photo by Staff Sgt. Kate Thornton
Read more from Sandboxx News
- That time Special Forces trained in the New Orleans Super Dome
- SOCOM’s new prop-driven attack plane can actually help counter China
- Special Forces test an Israeli mortar system that will make them more lethal and survivable
- Were there rivalries in the Delta Force ranks?
- This LVAW is SOCOM’s overpowered answer to the SMG
Related Posts
Sandboxx News Merch
-

‘AirPower’ Classic Hoodie
$46.00 – $48.00 Select options This product has multiple variants. The options may be chosen on the product page -

‘Kinetic Diplomacy’ Bumper Sticker (Black)
$8.00 Add to cart -

‘Sandboxx News’ Trucker Cap
$27.00 Select options This product has multiple variants. The options may be chosen on the product page
Steve Balestrieri
Related to: Breaking News, Special Operations

How an F-15E scored its only air-to-air kill… with a bomb

The military roots of Juneteenth and why we celebrate it
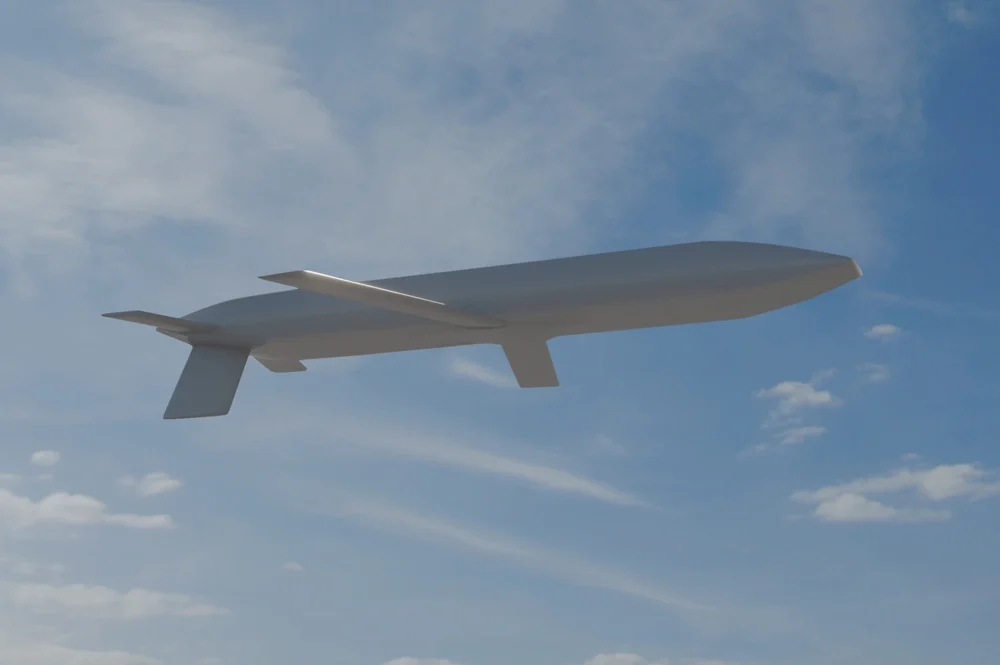
Air Force gives us a glimpse of its new AGM-181 LRSO nuclear missile

Israel wipes out Iranian F-14 Tomcats on the airstrip
Sandboxx News
-

‘Sandboxx News’ Trucker Cap
$27.00 Select options This product has multiple variants. The options may be chosen on the product page -

‘AirPower’ Classic Hoodie
$46.00 – $48.00 Select options This product has multiple variants. The options may be chosen on the product page -

‘AirPower’ Golf Rope Hat
$31.00 Select options This product has multiple variants. The options may be chosen on the product page -

‘Sandboxx News’ Dad Hat
$27.00 Select options This product has multiple variants. The options may be chosen on the product page
